Configure OpenVPN on CentOS using PrivateInternetAccess
I recently decided to start protecting myself against the evil spying of the US Government as well as all of the DMCA hounds that are crawling the internet. I have known about VPN's for quite some time, but I honestly never thought about using one. With all the leaks that Edward Snowden has been publishing, it got me thinking about my own online privacy, and how to best protect myself.
A trusted friend of mine has been using a VPN for several months now, and he gave me a really great recommendation on a VPN provider. PrivateInternetAccess.com is what he recommended to me, and it was a superb choice. Here is their webpage if you would like to check them out: https://www.privateinternetaccess.com/ They offer a really great and really fast VPN service for about $40 per year (at the time of this writing). They also accept Bitcoin as a payment method, which is great for remaining anonymous. Another reason to choose PIA (as they are often times referred to) is because they offer several egress point all over the Globe. Their service is fast as well. I am routinely seeing 20 to 30 meg speeds when using the US East coast egress points.
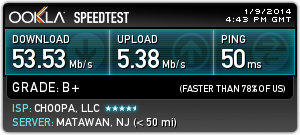
Here is a Speedtest.net graph to show a recent test:
Now, let's get started on getting this setup. I will provide step-by-step instructions below, and even provide some pre-built OpenVPN configuration files to make it even easier.
First you will need to signup with PrivateInternetAccess. Follow this link to signup and create your account: https://www.privateinternetaccess.com/pages/buy-vpn/ Once you get setup, they will email you with your credentials to use for the service. DON'T LOOSE THESE!
Then, you will need to perform the following to get CentOS or RHEL setup for the service.
-
Install OpenVPN on your machine. I am using CentOS 6.5 64 bit, but the instructions will be similar on other distros.
sudo yum install openvpn
-
Create a password file that contains your PIA credentials so that OpenVPN can use them to connect. These credentials are the ones the PIA emails to you. This will keep OpenVPN from prompting you for your VPN password when it connects. Set the permissions to 400 and give ownership to root.
echo "YOUR PIA USERNAME" > ~/.pia
echo "YOUR PIA PASSWORD" >> ~/.pia
sudo chown root:root ~/.pia && sudo chmod 400 ~/.pia
sudo mv ~/.pia /root/
-
Download the PIA configuration files. I have created the OpenVPN configuration files that will work with PIA already and included them in the command below. These config files are setup for all locations that PIA is currently offering, and I will do my best to keep them up to date.
wget http://www.gigahype.com/wp-content/uploads/2014/01/openvpn_configs.tar
-
Untar the config files and move them to the proper OpenVPN directory.
tar –xvf openvpn_configs.tar
sudo mv openvpn /etc/
-
Now, we need to create a server.conf file so that OpenVPN will know which of our PIA configs to look to. We do this by creating a symlink to whichever PIA config file we want to use. It's important to note that each of the PIA config files are designed for a certain region. This allows you to pick your egress point by country, state, or larger region. We will do an ls to list the files in the directory so you may choose whichever region you want to use.
cd /etc/openvpn
ls –l
(You can now see all of the regions that I have configured. Pick which one you want to use for the next step)
sudo ln -s /etc/openvpn/PICKYOURS.ovpn /etc/openvpn/server.conf
-
If you use Google DNS, OpenDNS, or even your ISP's DNS servers you expose yourself to DNS Leakage. DNS leakage occurs because the DNS providers are able to keep a record of all the sites that your computer requests IP's for. I highly recommend you google search the term "DNS Leakage" to get a better idea of it. If you want to mitigate DNS Leakage, PIA provides secure and private DNS servers. This step is totally optional, but I highly recommend doing this if you want to increase your security and anonymity. PIA's DNS servers are: 209.222.18.222 and 209.222.18.218 I will outline outline how to modify your DNS servers below:
sudo cp /etc/resolv.conf ~/resolv.conf.backup
sudo echo "nameserver 209.222.18.222" > /etc/resolv.conf
sudo echo "nameserver 209.222.18.218" >> /etc/resolv.conf
-
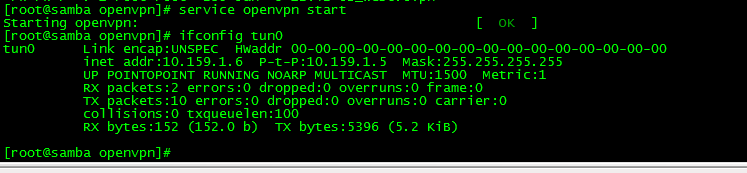
Now we will start the OpenVPN service and then make sure it is connecting to PIA and creating the proper VPN network adapter tun0
sudo service openvpn start
ifconfig tun0
(the ifconfig tun0 command should return the information about the VPN network. It will look something similar to the picture below)
-
If you would like to have OpenVPN always start at boot, you can do the following command. This is an optional step.
sudo chkconfig openvpn on
That's it! If everything went well, you know have OpenVPN fully configured on a headless CentOS machine and have set it up to connect automatically at boot. You can always double check to make sure it is working by looking for the tun0 adapter. If you have access to launch a web browser on the machine, you can point it to www.ipchicken.com and it will show you the external IP address you connected from. If you are going through the VPN adapter, it will be a different IP address than your ISP.
Please see my post on how to configure Transmission Bittorrent client to always send its traffic through the VPN connection to avoid being snooped on. You can find it here:
[…] http://www.gigahype.com/configure-openvpn-centos-privateinternetaccess/ […]
Thanks for the great walk through. I was working through it and this save me hours of troubleshooting.
Glad it helped!
Awesome write up! Just what I needed for my personal CentOS server and my existing account with PIA. Things were looking good, but the tun0 interface was not created after starting the service (the OpenVPN started with an [OK]). Any ideas?
Thanks for the guide.
Have done everything exactly. Got error - cannot access the password file. Moved password file into /etc/openvpn - everything is working now.
Now I wonder, what I did wrong, why the service cannot access the password file in /root directory.
I have another issue - when I switch resolv.conf, everything works until the connection break. After that openvpn cannot restore it, because it cannot resolve the address of the openvpn server. Switching back resolv.cong helps, but I would like to set up robust and unattended system.
Would appreciate any advice.
Thank you again.
Curious, how do you handle managing remote servers that block traffic from public VPNs such as PIA? For example, when I ssh out from PIA to a remote ssh server, it won't allow my ports to connect, even when I change them up due to not forwarding ports properly. Further, when I try to just hit the server(s) on cPanel or some such interface, likewise they frequently end up blacklisting the IP. I would like to hit certain IP address and/or domains simply by using my own IP so that I skip around the VPN for these such connections.
Did you figure out a way to do that readily so that you can quickly add ip's to the mix?
Frank,
Unfortunatley, we really have no control over what IP address a remote host blocks. However, Private Internet Access has a pretty large pool of IP's and you can always switch with VPN Egress point you want from their lists. Maybe try another egress point?
I'm sorry, I think I may have been unclear, let me try again: I am attempting to redirect outbound traffic from the gateway that is connected to PIA such that it will connect from my ISP's connection and therefore avoid using the OpenVPN PIA connection. So when I ssh out from any device / host behind the OpenVPN connected gateway / firewall, it will say "Oh, this is port XXXX (whether 22 or 22222, whatever I define it). I know that this is SSH traffic so I don't want to send this across the OpenVPN PIA connection; let's send it straight on through the ISP directly."
You may have to setup routes for which ever traffic you want to leave a different gateway.
thanks for the excellent guide. it is just what i needed to setup ubuntu server 12.04 with PIA and NOT have to use the gui. what is your Bitcoin addy? I will send you something for your excellent work.
Awesome! Glad it helped you out.
Since you asked for my Bitcoin address, you can use this one: 1PhpR1im61B9yizQKjNnJs27hhJ1Q8Tcei
Thanks for the write-up. I've had my connection up for awhile, but I'm digging down into the weeds a bit more to keep learning about VPN tunnels. Do you mind showing me the output of "ethtool tun0"?
Thanks in advance.
I get an error after I enter sudo service openvpn start:
Redirecting to /bin/systemctl start openvpn.service
Failed to start openvpn.service: Unit openvpn.service failed to load: No such file or directory.
Not sure what to do to fix this...
It was a straightforward and simple, yet concise PIA setup.
I am wondering if you know of any method by which I can light a little icon on the task bar while the PIA connection is live. It would be an important safety measure. Thanks.
I just used this guide to setup a new PIA OpenVPN connection on a minimal centos 7 install, and everything went well up until the very end, when I started getting rather odd failures on "sudo service openvpn start".
The following appeared in /var/log/messages:
openvpn[1408]: Options error: In [CMD-LINE]:1: Error opening configuration file: server.conf
Long story short: SELinux strikes again.
Here were the fixes:
1) Fix the SELinux file contexts for the /etc/openvpn directory:
sudo restorecon -Rv /etc/openvpn/
2) Fix the SELinux file context for /root/.pia:
sudo semanage fcontext -a -t openvpn_etc_t /root/.pia
sudo restorecon -v /root/.pia
... after that, everything worked perfectly! Thanks!
Nice post! Thank you.
I wrote a similar article but it uses NetworkManager (GUI) instead of command line. If you are interested take a look at https://techwords.io/en/configuring-pia-vpn-on-fedora/.